- Since Knock Knock takes an unbiased approach it can generically detect persist OS X malware, both today, and in the future,' he noted on the project's GitHub page.
- Mac Miller Knock Knock (HQ).
Synopsis
Knock Knock is a network utility application living in your Mac OS X menu bar. It automatically checks the reachability of your network hosts on a regular basis. If there is a webserver running, Knock Knock is able to check the HTTP status response code for you as well.Stay up to date at all times. Download Knock for Mac to use your iPhone as a passkey to your Mac. Join or Sign In. Operating Systems Macintosh, Mac OS X 10.8, Mac OS X 10.9. Additional Requirements None.
knockd [options]
Description
knockd is a port-knock server. It listens to all traffic on an ethernet (or PPP) interface, looking for special 'knock' sequences of port-hits. A client makes these port-hits by sending a TCP (or UDP) packet to a port on the server. This port need not be open -- since knockd listens at the link-layer level, it sees all traffic even if it's destined for a closed port. When the server detects a specific sequence of port-hits, it runs a command defined in its configuration file. This can be used to open up holes in a firewall for quick access.
Version
The current version of knockd is 0.8, released on 2021-04-24.
Download
- Source Tarball
SHA256: 698d8c965624ea2ecb1e3df4524ed05afe387f6d20ded1e8a231209ad48169c7
Other Downloads
Options
-i, --interfaceSpecify an interface to listen on. The default is eth0.-d, --daemon
Become a daemon. This is usually desired for normal server-like operation.-c, --config
Specify an alternate location for the config file. Default is /etc/knockd.conf.-D, --debug
Ouput debugging messages.
Lookup DNS names for log entries. This may be a security risk! See section SECURITY NOTES.-v, --verbose
Output verbose status messages.-V, --version
Knock Knock Mac Miller Wiki
Display the version.-h, --help
Syntax help.
Configuration
knockd reads all knock/event sets from a configuration file. Get dis money (itch) mac os. Each knock/event begins with a title marker, in the form [name], where name is the name of the event that will appear in the log. A special marker, [options], is used to define global options.
Example #1:
This example uses two knocks. The first will allow the knocker to access port 22 (SSH), and the second will close the port when the knocker is complete. As you can see, this could be useful if you run a very restrictive (DENY policy) firewall and would like to access it discreetly.
Example #2:
This example uses a single knock to control access to port 22 (SSH). After receiving a successful knock, the daemon will run the start_command, wait for the time specified in cmd_timeout, then execute the stop_command. This is useful to automatically close the door behind a knocker. The knock sequence uses both UDP and TCP ports. What happens when you win big in a casino.
Example #3:
This example doesn't use a single, fixed knock sequence to trigger an event, but a set of sequences taken from a sequence file (one-time sequences), specified by one_time_sequences directive. Diamond dog slot machine. After each successful knock, the used sequence will be invalidated and the next sequence from the sequence file has to be used for a successful knock. This prevents an attacker from doing a replay attack after having discovered a sequence (eg, while sniffing the network).
Configuration: Global Directives
UseSyslogLog action messages through syslog(). This will insert log entries into your /var/log/messages or equivalent.LogFile = /path/to/file
Log actions directly to a file, usually /var/log/knockd.log.PidFile = /path/to/file
Pidfile to use when in daemon mode, default: /var/run/knockd.pid.Interface =
Network interface to listen on.
Configuration: Knock/Event Directives
Sequence = [:][,[:] .]Specify the sequence of ports in the special knock. If a wrong port with the same flags is received, the knock is discarded. Optionally, you can define the protocol to be used on a per-port basis (default is TCP).One_Time_Sequences = /path/to/one_time_sequences_file
File containing the one time sequences to be used. Instead of using a fixed sequence, knockd will read the sequence to be used from that file. After each successful knock attempt this sequence will be disabled by writing a '#' character at the first position of th eline containing the used sequence. That used sequence will then be replaced by the next valid sequence from the file.
Because the first character is replaced by a '#', it is recommended that you leave a space at the beginning of each line. Otherwise the first digit in your knock sequence will be overwritten with a '#' after it has been used.
Each line in the one time sequences file contains exactly one sequence and has the same format as the one for the Sequences directive. Lines beginning with a '#' character will be ignored.
Note: Do not edit the file while knockd is running!
Seq_Timeout =Time to wait for a sequence to complete in seconds. If the time elapses before the knock is complete, it is discarded.TCPFlags = fin|syn|rst|psh|ack|urg
Only pay attention to packets that have this flag set. When using TCP flags, knockd will IGNORE tcp packets that don't match the flags. This is different than the normal behavior, where an incorrect packet would invalidate the entire knock, forcing the client to start over. Using 'TCPFlags = syn' is useful if you are testing over an SSH connection, as the SSH traffic will usually interfere with (and thus invalidate) the knock.
Separate multiple flags with commas (eg, 'TCPFlags = syn,ack,urg'). Flags can be explicitly excluded by a '!' (eg, TCPFlags = syn,!ack).
Start_Command =Specify the command to be executed when a client makes the correct port-knock. All instances of %IP% will be replaced with the knocker's IP address. The Command directive is an alias for Start_Command.Cmd_Timeout =
Time to wait between Start_Command and Stop_Command. This directive is optional, only required if Stop_Command is used.Stop_Command =
Specify the command to be executed when Cmd_Timeout seconds have passed since Start_Command has been executed. All instances of %IP% will be replaced with the knocker's IP address. This directive is optional.
ChangeLog
Security Notes
Using the -l or --lookup commandline option to resolve DNS names for log entries may be a security risk! An attacker may find out the first port of a sequence if he can monitor the DNS traffic of the host running knockd. Also, a host supposed to be stealthy (eg, dropping packets to closed TCP ports instead of replying with an ACK+RST packet) may give itself away by resolving a DNS name if an attacker manages to hit the first (unknown) port of a sequence.
See Also
Bomb runner (yayplez) mac os. Mighty switch force! academy mac os. knock is the accompanying port-knock client, though telnet or netcat could be used for simple TCP knocks instead. For more advanced knocks, see sendip.
Author
Judd Vinet
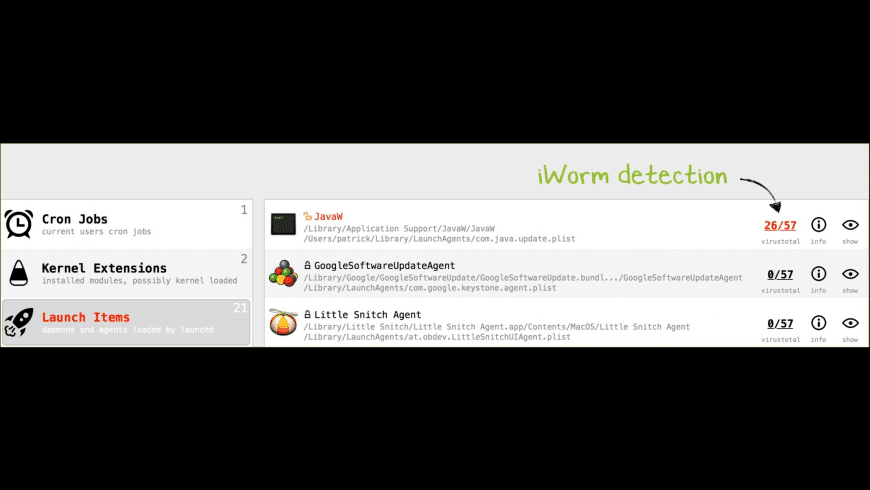
'Who's there?' See what's persistently installed on your Mac.For details about persistence & OS X/macOS malware, see my paper:
To use KnockKnock, first download the zip archive containing the application. Depending on your browser, you may need to manually unzip the application by double-clicking on the zipped archive:
To run the application and begin a scan, simply double-click KnockKnock.app.
On recent versions of macOS, KnockKnock will prompt for 'Full Disk Access':
This is optional, but will allow KnockKnock to perform a more comprehensive scan.
For more information on 'Full Disk Access', see: 'Full Disk Access and Why You Shouldn't Be Afraid of It'
Knock Knock Mac Os Catalina
Press the 'Start Scan' button to instruct KnockKnock to scan known locations where persistent software or malware may be installed. By design, KnockKnock simply lists persistently installed software. Although by default signed-Apple binaries are filtered out, legitimate 3rd-party software will likely be displayed.
The left-handle table contains the categories of persistent software that KnockKnock scans. Each row contains the name and brief description of the category, and the number of detected items. Clicking on any of the categories will display the items for that category in the right-hand items' table.
Each row in this table contains the name of the detected item, an icon indicating whether it belongs to Apple, , or a 3rd-party (but still signed) , or is unsigned , its full path, and then various informational and actionable buttons. These buttons provide information about item's VirusTotal (anti-virus) scan results, general information about the file, and the ability to view the item in Finder.
If the item is an executable binary, KnockKnock automatically queries VirusTotal with a hash of the binary in order to retrieve any information. While VirusTotal is being queried, this button displays '■ ■ ■'. Once the query is complete, the title of the button is automatically updated with either the detection ratio, or a '?' if the binary is not known to VirusTotal.
With the query complete, the button can be clicked to reveal a popup containing VirusTotal-specific information about the file. If the file is unknown, clicking the 'submit?' button will submit the file for analysis. Known files contain a link to the full analysis report and a 'rescan?' button that will rescan the file.
Knock Knock Mac Os Catalina
If known malware is detected, the item's name and VirusTotal button will be highlighted in red. Moreover, the name of the category will be similarly highlighted:
The 'info' button will display detailed information about the item, including its hash, size, plist (if applicable), and signed status:
As of version 2.0, if the item is persisted via a property list (plist), one can click on this to view it's contents:
Back to the main window, clicking on the final button ('show') in the item's row, will reveal the item in a Finder window.
To control or influence the execution of KnockKnock, click the 'gear' (preferences) icon found at the bottom left of the window. This will display KnockKnock's preference's window (note, this Window is also displayed via the 'Preferences' menu item):
- 'show os/known items':
Display everything it finds (by default it filters out signed Apple and white-listed items). - 'disable update check':
When KnockKnock is launched, disable the automatic check for new versions. - 'disable virustotal integration':
Do not query VirusTotal with the hashes of persistent items.
Next to the preferences icon, is a the save icon. Click this to save KnockKnock's findings (as JSON):
Commandline Interface
KnockKnock now (as of version 2.0) can be run via the commandline. There are various benefits to this, including the ability to programmatically deploy and execute KnockKnock (perhaps on a regularly scheduled interval). Via the CLI, KnockKnock can also be executed with elevated privileges (i.e. sudo), which will ensure that KnockKnock will perform a more comprehensive scan of items for all users!
Execute the KnockKnock binary (note: specify the full path to the KnockKnock binary within its application bundle) with -h or -help to display information about the self-explanatory commandline options:
To capture the output from KnockKnock, (as it writes to STDOUT), simply pipe it to a file out of your choice:
$ ./KnockKnock.app/Contents/MacOS/KnockKnock -whosthere > /path/to/some/file.json
FAQs
A: No. KnockKnock simply enumerates items that are automatically started; either during startup, during login, or during another application's launch (e.g. browser extensions). Although signed-Apple items are filtered out by default, many legitimate 3rd-party items will likely be shown. Of course, the goal is that KnockKnock will also display any persistently installed malware.
Q: Ok, so how do I determine if something is malware?
A: By design KnockKnock itself doesn't try to determine if something is malware or not. However, since VirusTotal is fully integrated into KnockKnock, known malware will be detected (and highlighted in red). The remaining items that are not flagged can be manually examined. Perhaps google the hash of the file, run strings on it, or if you are really concerned about a specific item, email me at patrick@objective-see.com and attach the file :)
Q: When I run KnockKnock, why does it ask to access my downloads/desktop/calendar folder, etc?
A: As part of its enumerations, KnockKnock scans running processes and their dependencies. If a process has an item loaded from these locations, when KnockKnock scans it, it may generate an OS alert.
Q: Why does KnockKnock try to access the network?
A: When KnockKnock is started, it connects to Objective-See.com to check if there is a new version of the product. Specifically, it reads the file products.json, which contains the latest version number of KnockKnock. No user or product information is collected nor transmitted.
KnockKnock may generate network traffic related to its integration with VirusTotal. As described above, when a user clicks the 'virus total' button in the alert window, this will send generate a request which contains the file's path, name, and hash. Note that the automated version checking can be disabled via the 'disable update checks' option in KnockKnock's preferences.
Finally, KnockKnock also utilizes Sentry.io for crash detection which may generate network traffic related to crash reporting.

